NAT Slipstreaming: Bypass Victim Firewall/NAT via Browser
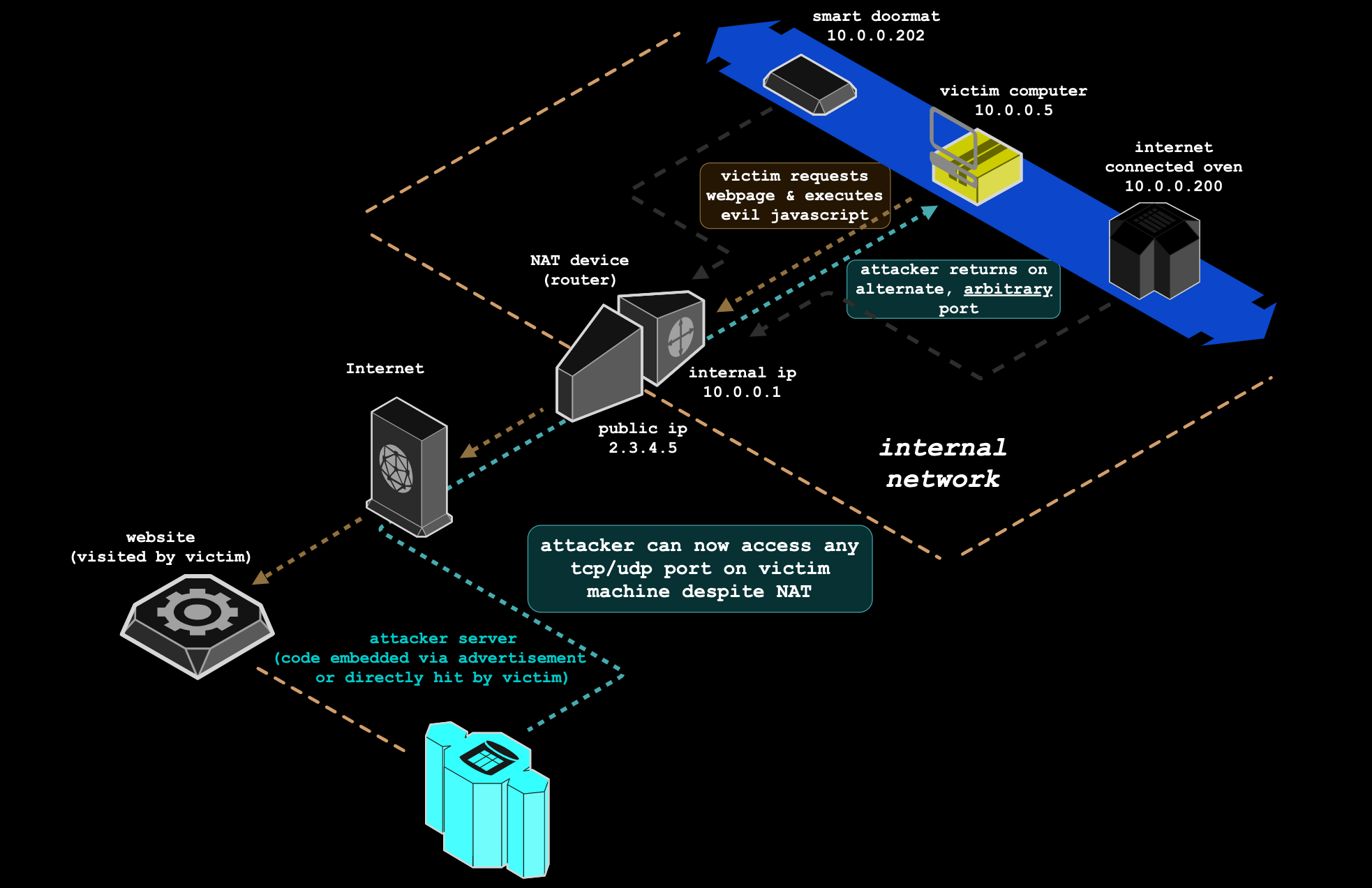
NAT Slipstreaming allows an attacker to remotely access any TCP/UDP service bound to any machine behind a victim's router, bypassing the victim's NAT/firewall (arbitrary firewall pinhole control), just by the victim visiting a website.
NAT Slipstreaming exploits the user's browser in conjunction with the Application Level Gateway (ALG) connection tracking mechanism built into NATs, routers, and firewalls by chaining internal IP extraction via timing attack or WebRTC, automated remote MTU and IP fragmentation discovery, TCP packet size massaging, TURN authentication misuse, precise packet boundary control, and protocol confusion through browser abuse.
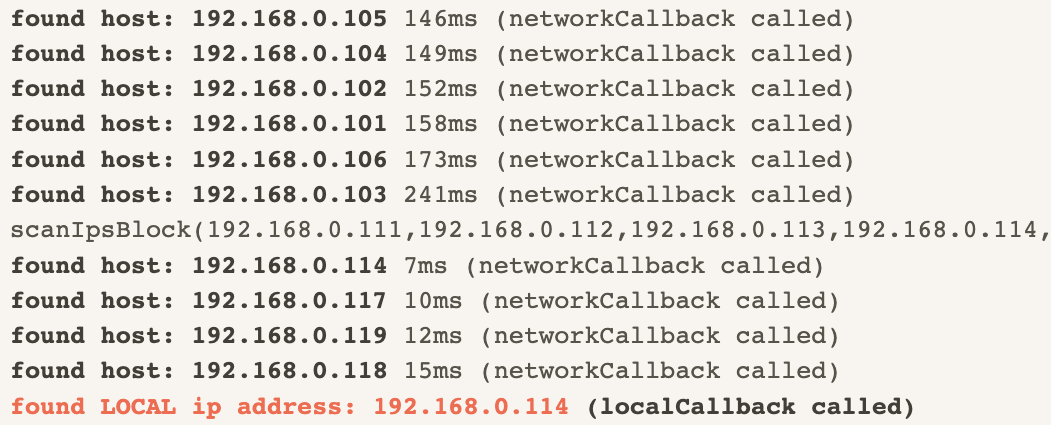
This attack takes advantage of arbitrary control of the data portion of some TCP and UDP packets without including HTTP or other headers; the attack performs this new packet injection technique across all major modern (and older) browsers, and is a modernized version to my original NAT Pinning technique from 2010 (presented at DEFCON 18 + Black Hat 2010). Additionally, new techniques for local IP address discovery are included.
Click here for more info.